Cost Monitoring Overview
env0 simplifies cloud cost management by integrating real-time monitoring directly into your IaC workflows. It precisely connects costs to specific changes, providing clear visibility across projects and environments. This allows teams to track budgets, identify anomalies, and make informed financial decisions, all while maintaining control within their existing processes.
Actual Cost
With cost monitoring enabled in env0, you will be able to see the cost of each Environment and Project you are running. The cost data will come directly from your cloud provider, and will include any costs incurred by your cloud resources, including fixed and usage-based costs.
Project CostsTo be able to see a project's costs you need to have the Edit Project Settings permission.
We utilize Terratag to automatically tag all of your cloud resources and determine exactly how much they cost over time.
Create cloud provider API credentials
In order to set up cost monitoring you will need to provide credentials that enable env0 to query your cloud provider's billing API. Below are guides for how to set up credentials in each cloud provider:
Credentials Management
When creating a credential in env0, it can be assigned to one of two scopes: Organization or Project.
- Organization Scope: When a credential is created via the organization credentials page (Organization Settings > Credentials), it is assigned to the
Organizationscope. This makes it available to all projects within the organization. - Project Scope: When a credential is created via the project credentials page (Project Settings > Credentials), it is assigned to the
Projectscope. This makes it available to that specific project and any of its sub-projects.
All credentials, regardless of scope, are visible on the organization credentials page. To create or update credentials in a specific scope, you must have the MANAGE_CREDENTIALS permission at that scope level (organization or project). By default, both Project Admin and Organization Admin roles include this permission.
For example, to create or edit credentials in the project "My Project," you need the MANAGE_CREDENTIALS permission for that project.
Use case example
A common reason to scope credentials is to separate access between environments. For instance, if you have distinct development and production projects, you can ensure that users in the development project do not have access to production credentials.
Enable cost monitoring
- Go to the Project Settings of the desired project
- Select the Credentials tab
- Check the appropriate cloud provider checkbox, and select the credential you created in the steps linked above
- Click Save
- To add the relevant tags to those environments' resources, you will need to redeploy all the relevant environments for which you would like to monitor costs
Accuracy and incurred costs
- env0 tags your Terraform resources, in order to query your cloud provider for the actual costs. You can see which tags are applied in the Terraform plan. Some resources might not be tagged, in which case the cost reported by env0 will be lower than expected.
- env0 will call your cloud provider's API to query the cost. This might incur additional charges from your cloud provider.
Viewing Costs
Environment Costs
After enabling cost monitoring for a project, all subsequent environments under that project would be monitored.
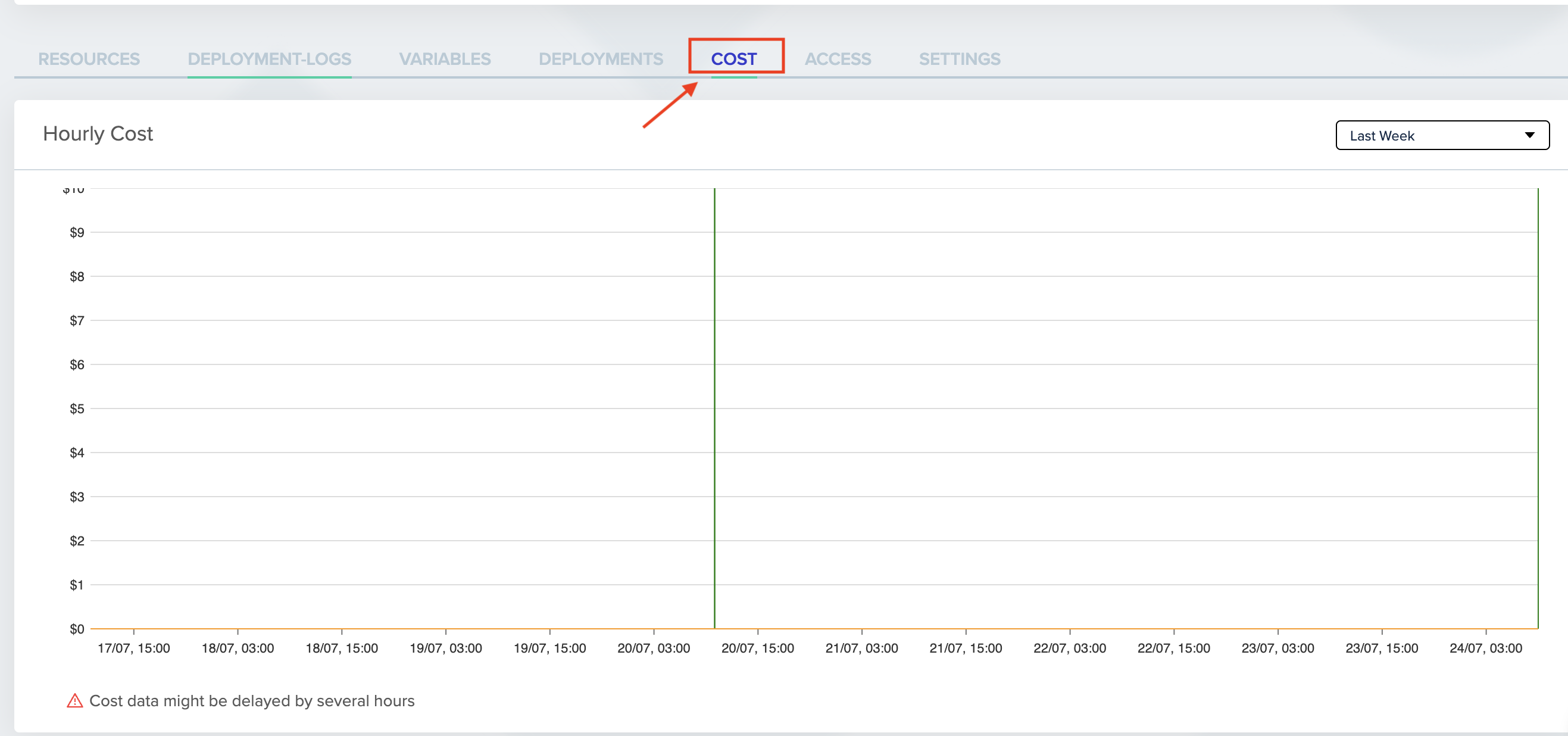
To view an environment's cost, go to that environment's page, and click on the COST tab.
Project Costs
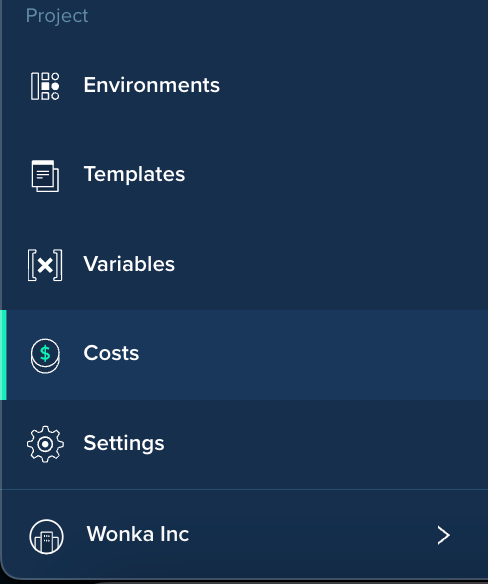
After enabling cost monitoring for a project, simply click Project Costs on the left-side panel
Organization Costs
After enabling costs for projects, you can view all of them under Organization Costs.
To get to the Organization Costs page, click on the Dashboards in the bottom left, then click the COST tab.
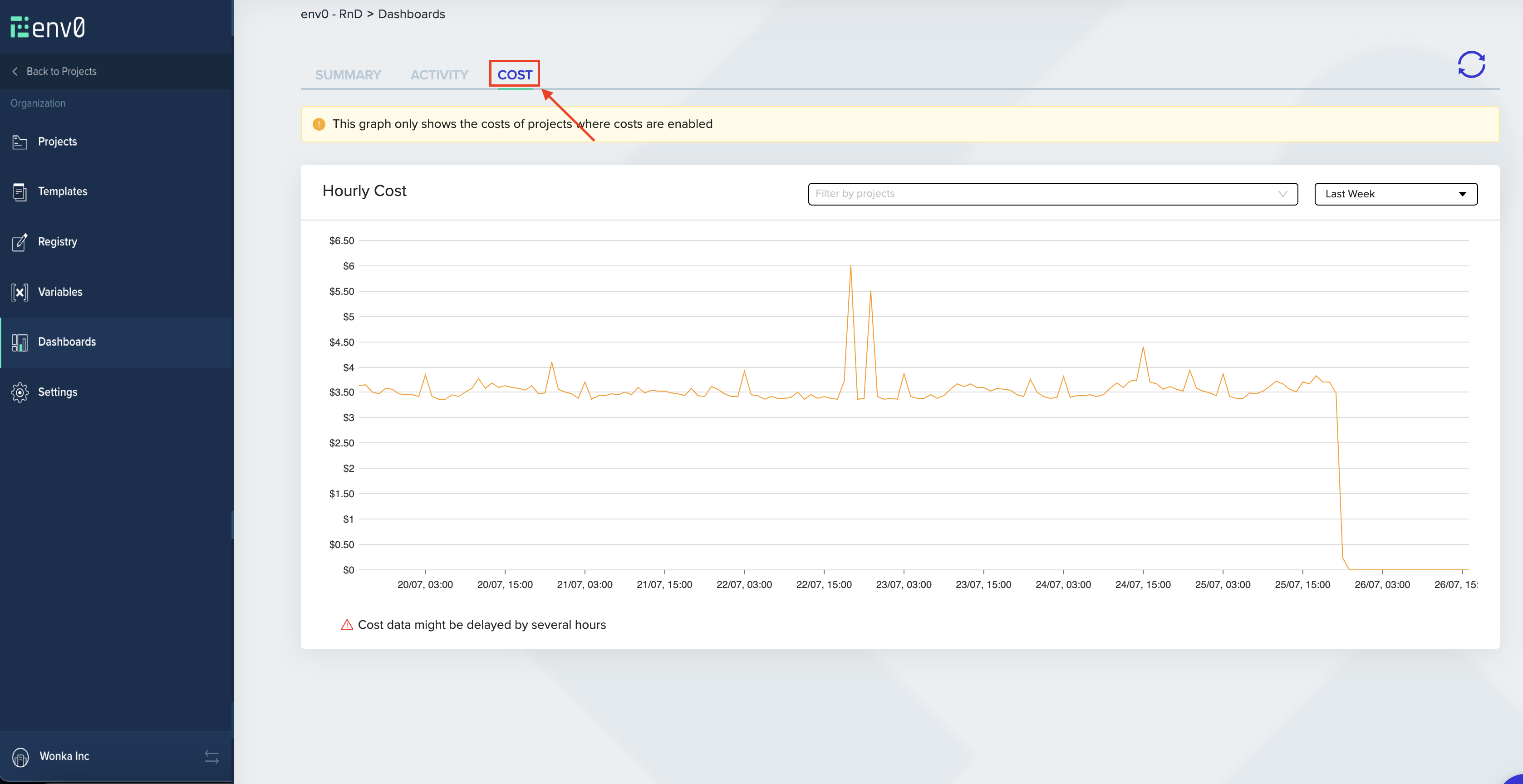
Project Based CalculationOnly projects with cost monitoring enabled would be accounted for.
Filter By Project
By default, the graph would display an accumulation of all project costs. You can filter by specific projects to view multiple projects' costs simultaneously. When chosen, each project's cost would be displayed separately.
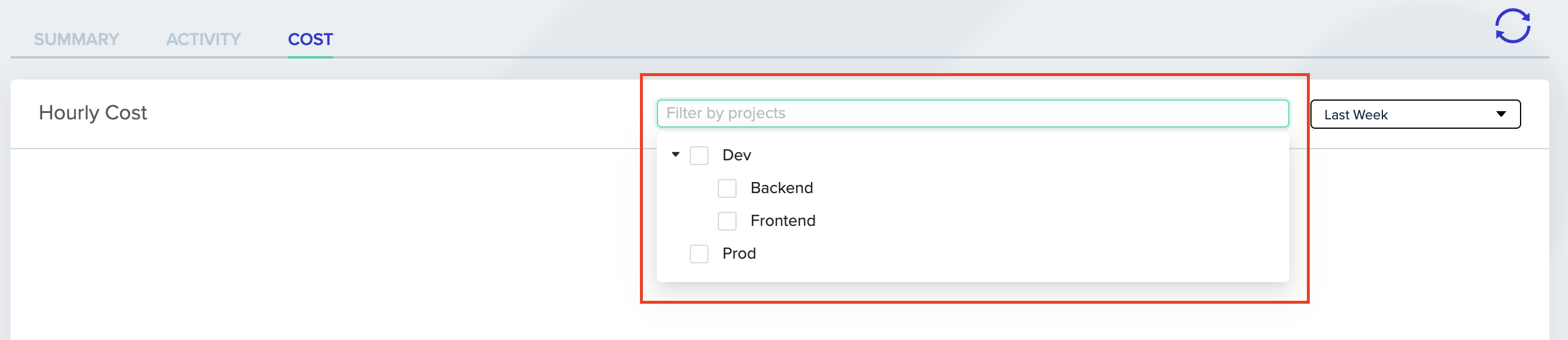
Project FilterIf a project title appears grayed out, it means that cost monitoring has not been configured for that specific project.
Updated 12 days ago
